Introduction to Two-factor Authentication.
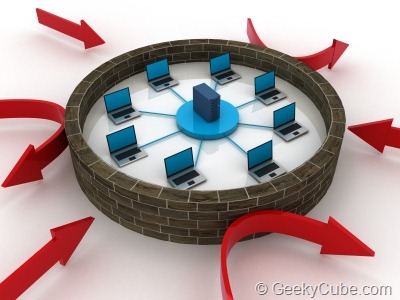
In recent times, one common problem that most of us have been facing is none other than the dilemma of being secure. In the recent past we have witnessed a large array of situations in which best of the best security softwares have failed to produce concrete results. As we all know, Facebook had recently reported around six lakh Fb logins being conciliated every 24 hours. So also, more than 760 companies were hit very badly and their private information was made available publicly. RSA’s SecureID, one of the most sophisticated security softwares also failed to fight back these hacking attacks. This adverse security situation has given rise to a pressing need of taking control of this scrupulous situation.
Some of the top level companies that are working towards building online security are Facebook, Google as well as Intuit. The first and foremost high end initiative that is taken by these companies is to introduce developed security means that come complete with text messaging as well as voice notifications. This one of its kind introduction is termed as two-factor authentication. The authenticity of this approach is way too higher since it requires the user to prove his or her identity is two separate ways. In case of the companies mentioned above the two different means of identification include a user password coupled with an authentication code that is made available over phone calls or text messages.
Working of Two-factor Authentication.
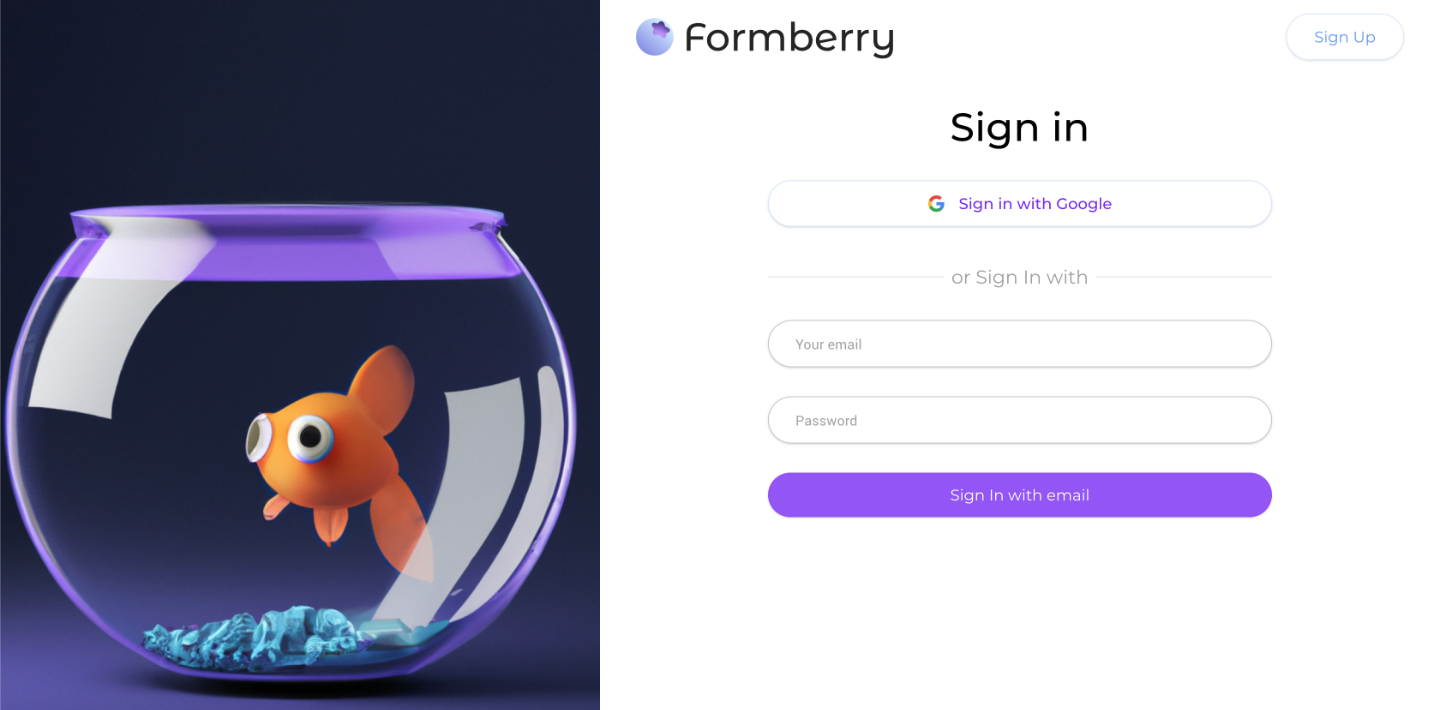
The working of Two-factor phone based authentication is absolutely straight-forward and easy. First and foremost you need to sign-up for the same wherein you will have to provide your cell phone number of landline number. In the next step when you login to your device or browser you will have to enter the authentication code that is provided either over messages or dictated over a phone call. Once you enter your authentication code you will get access to your account. Some of the companies require you to produce the authentication code every time that you log in while some others like Google expect you to share your authentication code once every thirty days.
One distinguishing element with respect to Facebook is that it requires you to feed in the authentication code not only when you plan to sign in to your account, but also during every occasion when you are using a third party app such as the game Farmville.
Two-factor Authentication comes across as a superior security tool that is absolutely powerful. If you are making use of this tool, then you do not need to worry about your account being hacked because even if the hacker is able to get access to your password, getting their hands on your authentication code is next to impossible.
Benefits of using Two-Factor Authentication along with Messages & Voice notification
There are two major benefits of making use of text messages and voice notifications in association with Two-factor Authentication.
The new model of Two-factor Authentication is known to provide massive amount of convenience to all its users. In the older model, individuals had to necessarily carry a USB or token in order to keep this tool active. However, the new model requires you to only be in sync with your mobile phones. Most of us are absolutely well-versed about the general usage of cell phones. Texting has become one of our common favorite activities. The above mentioned plus points have offered a good deal of ease as far as usage of two-factor authentication is concerned.
Secondly, when security comes with affordability then in that case this is the best situation that we can be in. The best part about two-factor authentication is that it is priced so nominally that companies can provide this to both their employees as well as customers at large. It is advisable to make use of Twilio for the sake of Two-factor Authentication application.
On an overall level it is vital to take care of two-factor authentication in order to keep your passwords secure. The common problems that occur, which can be easily avoided include setting passwords that are not easy to guess and secondly employees setting passwords that are uncommon and unrelated to each other.
The above article gives a realistic account about two-factor authentication.
I am Rahul a content writer and a Professional Blogger. I am certified with ST0-153 test questions which are very popular these days and have a great scope in the field of IT Certification. I always like to take certification exams and now I have planned to pass ST0-151 test questions. These kinds of exams could secure your future as well as your job.