WHAT IS IAM?
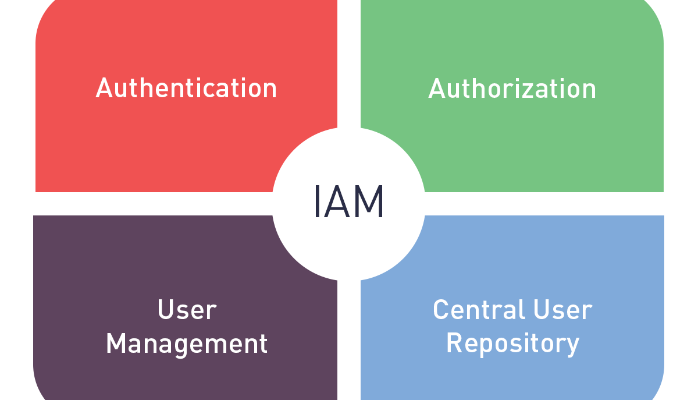
More businesses are becoming aware of the need for identity access management, or IAM to use the abbreviated term. With increased digital and electronic identities now prevalent across most industries it has become essential that a framework is created to manage these effectively and that’s where IAM comes in. But what exactly is it?
By using IAM technologies systems managers within an organisation can regulate user access to critical data so that users are only given certain administrative rights depending on their allocated role in an business. Obviously many external users now need access to internal systems making the need for IAM even more crucial.
Typical access rights will be familiar to most people who use digital technologies and may include giving an individual the capacity to create, view or modify a file or dataset. How extensive the rights are will depend on the person’s job role, responsibility and authority level within an organisation or will be subject to what they need access to if they are an external user.
Types of systems utilised as part of IAM processes can include multi-factor authentication, which as it sounds needs multiple types of authentication to login, and also single sign-on, and these methods are accessed in various ways, sometimes on site or through a cloud-based model for instance.
KEY FEATURES OF IAM:
Good identity access management needs to factor in the essential tools and functions to capture and monitor user login information, oversee the database of users and hierarchy of access and have a mechanism for managing the process of granting and removing access rights to different individuals.
Other considerations need to be speed and effectiveness of systems so that business functions are not impaired or slowed down. As an example, rather than an individual trying to synchronise requests for access to job roles it is necessary to have a centralised function for this task so that it can be carried out automatically thus saving time and possibility of error.
However, the automatic functions need to have some flexibility for modification as it is not always as straightforward as matching job roles and titles to access levels, therefore a request process for modified approvals should also be put in place as certain employees may need slightly differing access levels depending on their work tasks.
BENEFITS OF IAM:
- Data Security: Good IAM systems can prevent significant data breaches.
- Consistent user access rules: Only the right people have access at the right level.
- IT Helpdesks: Reductions in calls as more users self-manage.
- Enhanced business productivity: Reduction in costs and less complexity in terms of security processes.
- Business credibility: Many governments, overarching bodies and regulators expect that enterprises will have secure IAM systems in place.
WHY YOU CAN’T DO WITHOUT IAM:
As enterprises become increasingly complex with multiple flows of digital business data both internally and externally, access and security in the IT environment have had to evolve rapidly to meet the challenge of the many layers of access required. IAM has become not only needed but increasingly essential to ensure effective and secure business operations.